What Is Network Segmentation?
Network segmentation is the practice of dividing a computer network into smaller, isolated subnetworks — each functioning as its own security zone with enforced access controls. Rather than treating every device on your network as equally trusted, segmentation creates defined boundaries: a compromised device in one zone cannot freely communicate with systems in another.
When a threat actor gains initial access through phishing, stolen credentials, or an unpatched vulnerability, their next move is typically lateral movement — scanning and pivoting across your network to reach sensitive data, domain controllers, or payment systems. Network segmentation is the primary architectural control that stops that pivot.
For small businesses, healthcare organizations, and tax professionals, network segmentation delivers some of the highest return of any security investment. It reduces your attack surface, limits breach damage, and is required — not just recommended — by several major regulatory frameworks including PCI DSS 4.0, HIPAA, and NIST SP 800-171.
Network Security By the Numbers
IBM Cost of Data Breach Report 2024
Time to identify and contain breach
Breaches using network traversal techniques
The Cost of an Unsegmented Network
Organizations without proper network segmentation face exponentially higher breach costs and longer recovery times. When attackers gain access to a flat network, they can move freely between systems, escalating privileges and accessing sensitive data across the entire environment.
The Verizon 2024 Data Breach Investigations Report found that lateral movement techniques appear in the majority of sophisticated attacks. Without segmentation, a single compromised endpoint can lead to domain admin compromise, complete data exfiltration, and ransomware deployment across the entire network.
How Network Segmentation Works
Network segmentation creates enforced boundaries between groups of devices using routers, firewalls, switches, and software-defined networking controls. Traffic crossing a segment boundary is inspected against a defined policy — only explicitly authorized communication passes through. Everything else is denied by default.
Think of it as internal zoning for your network. Your guest Wi-Fi, employee workstations, servers hosting sensitive data, and internet-facing services each occupy their own zone. A compromised workstation in the employee zone cannot initiate connections to your database server or domain controller without first passing through a policy checkpoint.
Network Segmentation Implementation Steps
Inventory Network Assets
Map all devices, applications, and data flows. Document what communicates with what and identify sensitive data repositories.
Define Security Zones
Group assets by function, trust level, and compliance requirements. Separate public-facing, internal, and sensitive systems into distinct zones.
Design Traffic Policies
Create access control rules governing communication between zones. Default to deny-all, then add explicit allow rules for necessary traffic.
Implement Technical Controls
Deploy VLANs, firewalls, and routing policies to enforce segmentation boundaries. Start with high-impact, low-complexity segments first.
Monitor and Validate
Test policies to ensure they block unauthorized traffic while allowing legitimate business functions. Use network monitoring tools to verify enforcement.
Maintain and Evolve
Regularly review and update policies as business requirements change. Add new systems to appropriate segments and remove obsolete rules.
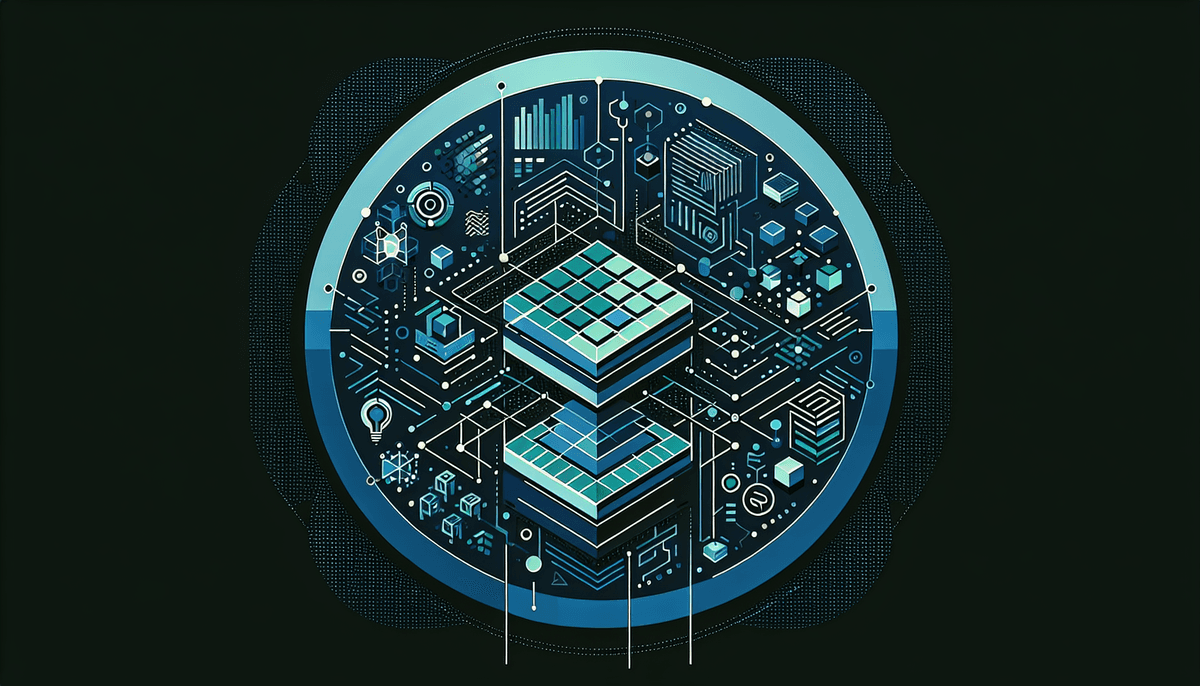
The Four Main Types of Network Segmentation
VLANs (Virtual Local Area Networks) — Logical segmentation at Layer 2 of the network stack. VLANs partition a single physical switch into multiple virtual segments. This is the most accessible starting point for small and mid-sized organizations — it requires managed switches but minimal additional hardware investment.
Subnets — IP address-based segmentation at Layer 3. Subnetting divides your IP address space into distinct networks, with routing rules and access control lists (ACLs) governing traffic between them. VLANs and subnets are frequently deployed together: VLANs handle Layer 2 isolation while subnets provide the IP-level boundaries that firewalls and routers enforce.
Demilitarized Zone (DMZ) — A dedicated buffer network segment that separates internet-facing systems — web servers, email gateways, remote access portals — from your internal network. Even if an attacker compromises a DMZ system, a second firewall stands between the DMZ and your internal environment, blocking direct access to internal servers and data.
Microsegmentation — Fine-grained, software-defined isolation applied at the workload or application level. Microsegmentation enforces policies down to individual virtual machines, containers, or application components, making it the most granular approach for cloud and hybrid environments. Software-defined networking platforms from vendors like VMware, Illumio, and Akamai deliver microsegmentation through agent-based or network-based policy enforcement.
Most organizations start with VLANs and firewall-enforced zones, then advance toward microsegmentation as infrastructure complexity grows. The right mix depends on your architecture, compliance requirements, and operational capacity.
Network Segmentation and Regulatory Compliance
Multiple federal and industry regulations treat network segmentation as either a required control or the primary mechanism for satisfying access control mandates. If your business operates in a regulated industry, segmentation is a compliance obligation with real enforcement consequences — not an optional enhancement.
PCI DSS 4.0 — The Payment Card Industry Data Security Standard (PCI DSS) 4.0 uses network segmentation to define the scope of your Cardholder Data Environment (CDE). Effective segmentation isolates systems that store, process, or transmit cardholder data from all other systems — dramatically reducing the number of systems subject to full PCI controls. Without proper segmentation, your entire network falls within PCI scope, multiplying compliance burden and remediation costs.
HIPAA Security Rule §164.312 — Under HIPAA Security Rule §164.312(a)(1), covered entities must implement technical access controls that restrict access to electronic protected health information (ePHI) to authorized users and software programs. Network segmentation is the standard architectural control used to meet this requirement, isolating systems that process ePHI from general-purpose workstations and internet-facing services.
NIST SP 800-171 Rev. 3 — NIST SP 800-171 Rev. 3 governs protection of Controlled Unclassified Information (CUI) for federal contractors. Control 3.13.3 requires separation of system and user functionality, while Control 3.13.5 mandates subnetworks for publicly accessible system components. Organizations applying the NIST incident response framework also benefit from segmented architectures — isolated zones make detection, analysis, and containment significantly more tractable during active incidents.
FTC Safeguards Rule — Tax preparers, financial advisors, and other non-bank financial institutions covered by the FTC Safeguards Rule must implement access controls as part of their written information security programs. Network segmentation is listed explicitly as a qualifying technical safeguard.
Common Segmentation Mistakes That Undermine Security
Even well-designed segmentation projects fail when teams skip foundational steps or treat network segmentation as a one-time deployment rather than an ongoing operational discipline. The most frequent failure modes:
Exception creep that swallows the design — Every exception to your segmentation policy creates a potential lateral movement path. Rule changes should require documented justification and periodic review, not a quick fix to resolve a helpdesk ticket.
Neglecting east-west traffic — Most teams focus on north-south traffic (internet-to-internal) and overlook east-west traffic (server-to-server, workstation-to-workstation). The Verizon 2024 Data Breach Investigations Report found lateral movement present in the majority of sophisticated breach cases — these techniques are catalogued in the MITRE ATT&CK framework.
Leaving IoT and OT devices on the main network — Smart building systems, IP cameras, printers, and operational technology devices are frequent initial access vectors. These devices rarely support enterprise security controls and should live in dedicated isolated segments, never on the same VLAN as workstations or servers.
No validation after changes — Networks evolve constantly. New SaaS integrations, cloud services, and remote access tools create new traffic flows that silently bypass existing segment policies unless security teams actively track and validate changes against the intended architecture.
Why This Matters
Network segmentation is not optional for regulated industries. PCI DSS, HIPAA, and federal contractor requirements mandate access controls that segmentation provides. Poor segmentation means compliance failures, expanded audit scope, and higher breach costs.
Network Segmentation as the Foundation for Zero Trust
Network segmentation is the architectural starting point for zero trust security. Legacy perimeter models granted broad trust to any traffic that made it inside the network boundary. Zero trust eliminates that assumption — requiring verification of every user, device, and connection regardless of network location or how access was obtained.
Segmentation establishes the isolated zones that zero trust policies govern. You cannot enforce per-workload identity-based access policies without first isolating workloads into defined segments. Organizations mature along a clear spectrum: VLANs and firewall rules establish the foundation; software-defined microsegmentation with identity-aware policy enforcement reaches a fully realized zero trust architecture.
If your organization is actively managing a breach or preparing response playbooks, your incident response plan should explicitly reference which network segments to isolate during containment — this is where segmentation proves its value in the worst-case scenario.
Need Expert Guidance?
Our network security team has helped 2,000+ organizations design and implement compliant segmentation architectures.
Get Your Network Segmentation Assessment
Our security engineers will map your current network architecture, identify segmentation gaps, and deliver a prioritized remediation roadmap tailored to your compliance requirements and risk profile.
Frequently Asked Questions About Network Segmentation
Network segmentation divides your computer network into smaller, isolated sections with controlled access between them. Instead of all devices trusting each other, segmentation creates security zones where devices must be explicitly authorized to communicate across zone boundaries. This prevents attackers who compromise one device from freely moving to other systems.
PCI DSS 4.0 does not explicitly require network segmentation, but it is the standard method for reducing compliance scope. Effective segmentation isolates your Cardholder Data Environment (CDE) from other systems, dramatically reducing the number of systems subject to PCI controls. Without segmentation, your entire network may fall within PCI scope.
Traditional network segmentation uses firewalls and VLANs to create zones at the network level. Microsegmentation provides much finer control, creating security policies down to individual applications, virtual machines, or containers. Microsegmentation is typically software-defined and can enforce policies based on workload identity rather than just network location.
Network segmentation limits ransomware spread by preventing encrypted malware from moving between network zones. When ransomware compromises a workstation in one segment, segmentation policies block its access to file servers, domain controllers, and backup systems in other segments. This containment limits damage and preserves recovery capabilities.
A DMZ (Demilitarized Zone) is a network segment that acts as a buffer between the internet and your internal network. Internet-facing services like web servers, email gateways, and VPN endpoints are placed in the DMZ. Even if these systems are compromised, a second firewall blocks direct access to internal networks and sensitive data.
Network segmentation works with firewalls, not instead of them. Firewalls are often the enforcement point for segmentation policies, controlling traffic between network segments. You need both perimeter firewalls (protecting against external threats) and internal firewalls or access controls (enforcing segmentation between internal zones).
Network segmentation costs vary widely based on your current infrastructure and approach. VLAN-based segmentation using existing managed switches may cost $5,000-15,000 for a small business. Firewall-enforced segmentation typically ranges from $15,000-50,000. Enterprise microsegmentation platforms can cost $100,000+ but provide the most granular control and automation capabilities.
Network segmentation is a foundational technology that creates isolated network zones. Zero trust is a security architecture that assumes no implicit trust and verifies every access request. Segmentation provides the isolated zones that zero trust policies govern — you cannot implement zero trust without first having proper network segmentation in place.
Schedule
Want personalized advice?
Our cybersecurity experts can help you implement these best practices. Free consultation.